Microsoft Compliance Configuration Analyzer
Microsoft Compliance Configuration Analyzer
In this short post, we will look at MCCA (Microsoft Compliance Configuration Analyzer). MCCA is a PowerShell-based tool that exports your current Microsoft 365Complaince configuration and validates them against Microsoft 365’s recommended best practices.
Some of the controls which forms part of the best practices include regulations and standards for data protection and data governance.
Perquisites for MCCA
- Exchange Online PowerShell Module (v2.0.3 or higher)
How to Install MCCA:
To get started with the Installation, you will have to launch Windows PowerSell and install the MCCA module.
Install-Module -Name MCCAPreview

Now that you have the tool installed, lets go ahead and run the following to generate the first MCCA report.
Get-MCCAReport
You need to accept the terms and read the warning about the tool, if you happy select Yes.

You will be prompted to enter your username and a popup for Microsoft 365 authentication windows will open.


The Report will take between 2-5 minutes to complete, once completed the html file will open in your browser. It will look as follows:

This report is stored locally in the directory C: Users username AppData Local Microsoft MCCA. A new report will be generated each time you run the tool and previous versions of the report can be found in the same location.
Report Breakdown.
You might notice that in the report you have the following message.
![]()
This message indicates that the report was not based on the specific region. To customize the report to be based on your Geo location, you will have to specify that in the PowerShell command when running the command.
Your geolocation selection is used to assess sensitive information types (SITs) which are relevant to that geolocation and generate a report that aligns to your country or region. Choose geolocations based on data you have in your tenant.
Each Geo location is associated with a code, all current codes can be found below.

Let’s go ahead and rerun the report based on UK and European standards.
Get-MCCAReport -Geo @(4,14)

You will notice that the report now has a note in it, indicating the report is based on the geo regions we specified when running the report.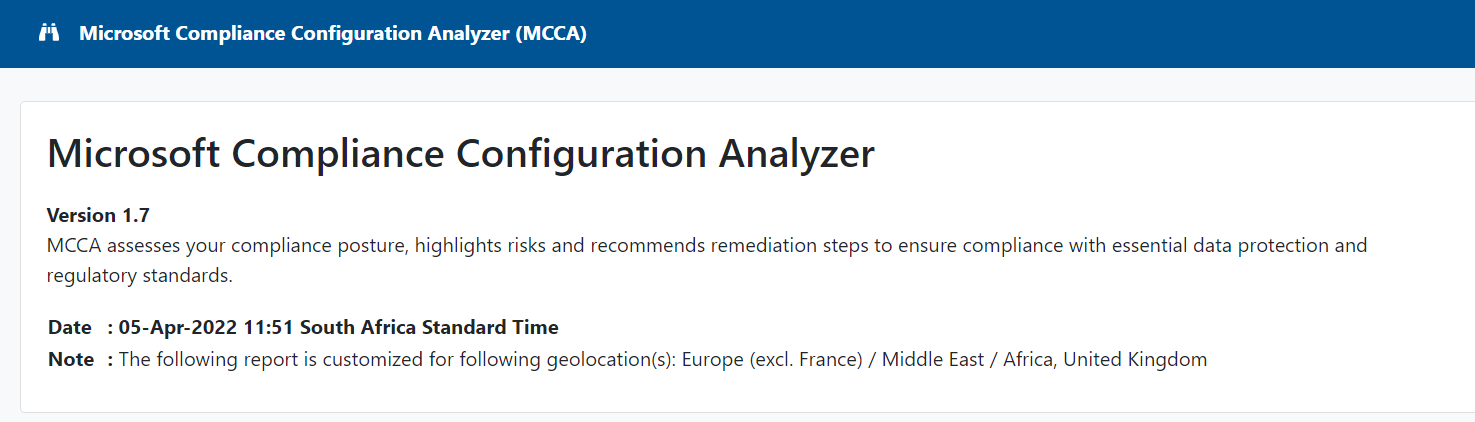
MCCA evaluates your current configurations against the recommended improvement actions in Compliance Manager. Any improvement action identified by the MCCA tool as needing attention will be listed in this section.
Next to each Microsoft solution are color-coded boxes indicating the number of items that correspond to improvement actions in Compliance Manager. The actions are broken down into three status states:
- OK: the actions that meet recommended conditions and need no attention at this time
- Improvement: actions that need attention
- Recommendation: actions that don’t need attention, but for which we recommend best practices
Select a box to view improvements and recommendations.
By selecting Client-side sensitivity labels, we can now see that there are no label policies in place. Part of the recommendation as you can see below is useful links so you can implement what is missing or recommended.

For DLP, there’s a Remediation Script button that gives you a pre-generated PowerShell script based on what’s recommended. You can copy and paste it directly in your PowerShell console. It will create a DLP policy in test mode
Here is an example of that PowerShell script:

Complete script can be found in the report section.
For more information about the MCCA tool, you can visit the Github page. Here you will find detailed information about the tool.
#HappyReporting.